The Problem:
Having visibility and\or control over who can and can’t copy, send, attach your company’s data, and or client information to emails, or copy it to a usb drive, or even print it out and take a physical copy with them.
It also is becoming more prevalent due to the EU getting strict on GPDR rules and laws. These may be enforced in NZ at some stage but to date the govt hasn’t given any indication on this. Companies that trade with EU and or USA customers
A common enquiry we hear:
Are we able to see what a staff member has downloaded to their computer? The intent would be then getting this on USB or via personal email to take and use this information for personal use. Reason we ask is how do we protect ourselves when someone leaves, and they may take key information with them. We have someone leaving soon, and in the past an employee took client lists and contacts.
The Solution: DLP – Data Loss Prevention
So what is DLP?
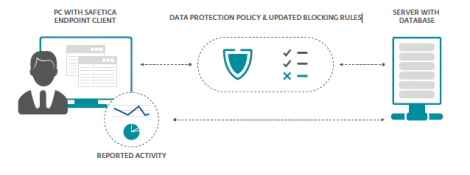
DLP is a method of inspecting and keeping sensitive data from leaving the allowed perimeter. DLP systems are only concerned with the data passing over some kind of gateway device, such as through emails, usb drives, instant messages and Web 2.0 applications.
It can identify sensitive data like credit card info, and can be configured to monitor specific locations and\or data types.
DLP – Data Loss Prevention Agents. These are deployed to all machines that need protection and management. This means they can be controlled, restricted, and reported on.
The agent can be set to not be visible on the machine, so the end user can’t disable it.
Key Features
| Complete Data Leak Prevention | Covers all data leaks channels while being easy to install and operate. |
| Trends & Productivity Profiling | Warns company management in the event of sudden changes in employee activity and shows productivity changes by department over time. Both changes are indications of possible security risks. |
| Activity Reporting | Uncovers security breaches on many fronts by checking all user activities for signs of potential danger, even before the actual transfer of data. |
| E-mail DLP | Ensures protected data stays out of the wrong mailbox. Records where sensitive files have been sent and stores this information for future reports. |
| Application Control with Time Rules | Enables selected package of work related applications and blocks others for a more secure environment. Applications can be made available only for a specified time frame. |
| Web Filtering | Easily enforces company AUP (Acceptable Use Policy) with carefully preselected categories and keyword filtering. |
| Print Control | Limits what can be printed and by whom with quotas for individual users and departments. |
| Device Control | Prevents employees from connecting unauthorized devices at work. Common ports can be enabled for particular devices or blocked for all of them. |
| Encryption Management | Offers Full Disc Encryption or encrypts whole partitions and creates local or network virtual drives for secure file storage. In addition to password and key access methods, offers secured Travel Disks and an “encrypt when copying out” feature for data leaving the Safe Area. |
| Informative & Testing Mode | Helps companies progressively integrate data protection by enabling tests for all “what-if” situations without halting business processes. |
| On the Fly Data Classification | Protects new information immediately after a classified file is created or received. |
| Unified Management Console | Management Console enables one-stop security management and reporting, integrates all company data protection, reporting and blocking policies. |
| SSL/HTTPS Inspection | Checks and protect secured communication lines including websites using HTTPS protocol, IM applications with secured connections and secured email transmission. |
| Minimal Total Cost of Ownership (TCO) | Frees users from the need to buy extra security appliances. The endpoint agents deployed also provide Data Leak Prevention features for company networks. |
| Flexible Use | Covers any application, Instant Messaging protocol or webmail service thanks to its unique universal approach. |
How it works:
If you’d like to know more about Data Loss Prevention, or would like to get protected, Call us today to get protected.
09-9735509 or support@wizard-it.co.nz